-
Notifications
You must be signed in to change notification settings - Fork 10.3k
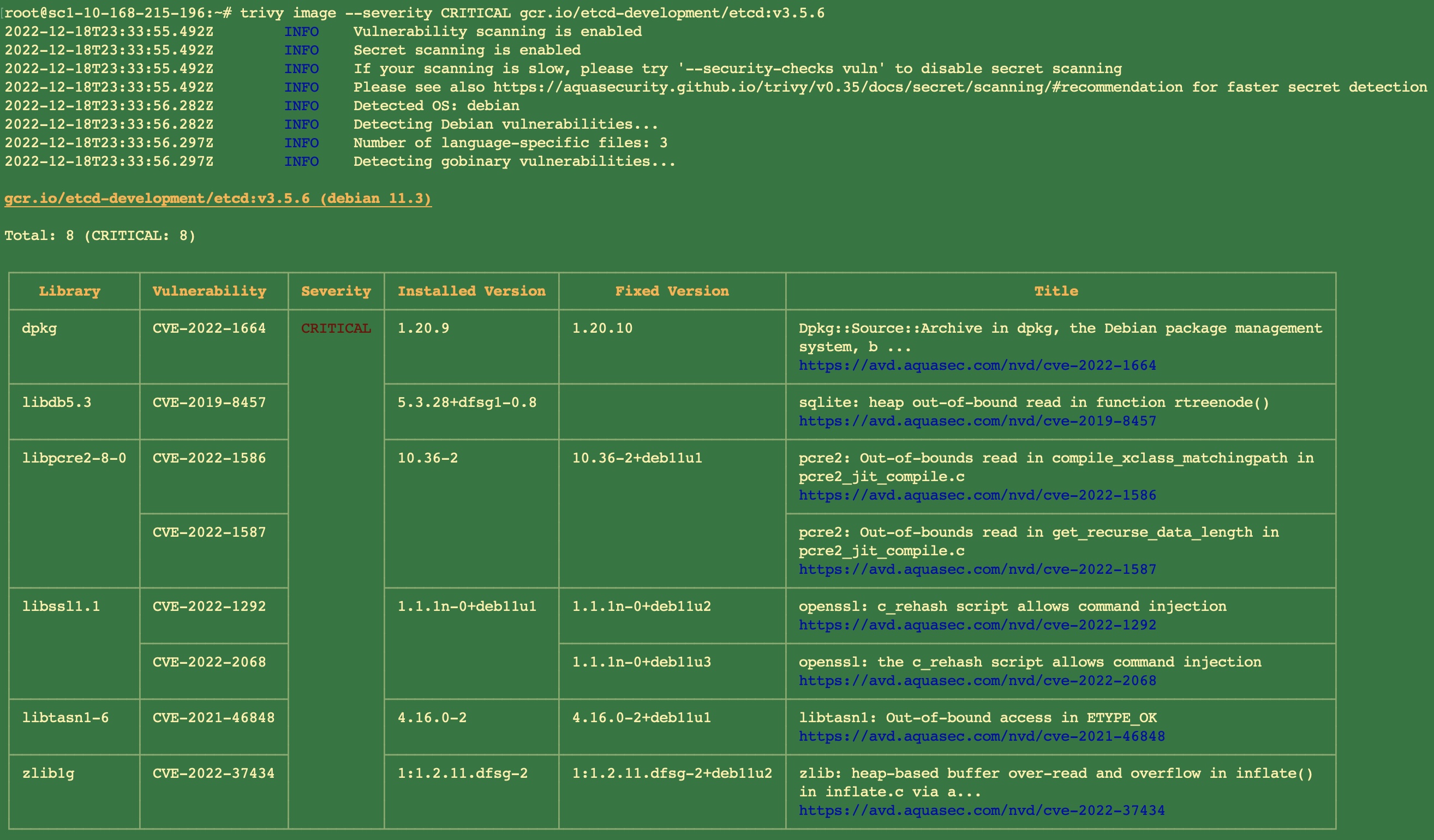
[3.5] Security: use distroless base image to address critical Vulnerabilities #15016
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Conversation
|
Note: I have confirmed that there is no critical Vulnerabilities any more after using the distroless base image. |
Command: trivy image --severity CRITICAL gcr.io/etcd-development/etcd:v3.5.6 -f json -o 3.5.6_image_critical.json Signed-off-by: Benjamin Wang <[email protected]>
d38d450 to
b766840
Compare
 fuweid
left a comment
fuweid
left a comment
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
LGTM(non-binding)
 ptabor
left a comment
ptabor
left a comment
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Please mention it in a changelog.
It's a potentially breaking change (if someone installs own scripts on top of etcd image).
Yes, I will update the changelog when I finish all the Vulnerabilities (including HIGH and critical) |
[3.5] Security: use distroless base image to address critical Vulnerabilities
Command:
See report:
Signed-off-by: Benjamin Wang [email protected]
Please read https://github.com/etcd-io/etcd/blob/main/CONTRIBUTING.md#contribution-flow.
cc @mitake @ptabor @serathius @spzala