Open security scanner for AI supply chain — agents, MCP servers, packages, containers, cloud, GPU, and runtime.
Start with the demo, then choose the entrypoint that matches your first job: repo scan, image scan, cloud posture, fix plan, dashboard, or runtime review.
CVE-2025-1234 (CRITICAL · CVSS 9.8 · CISA KEV)
|── [email protected] (npm)
|── sqlite-mcp (MCP Server · unverified · root)
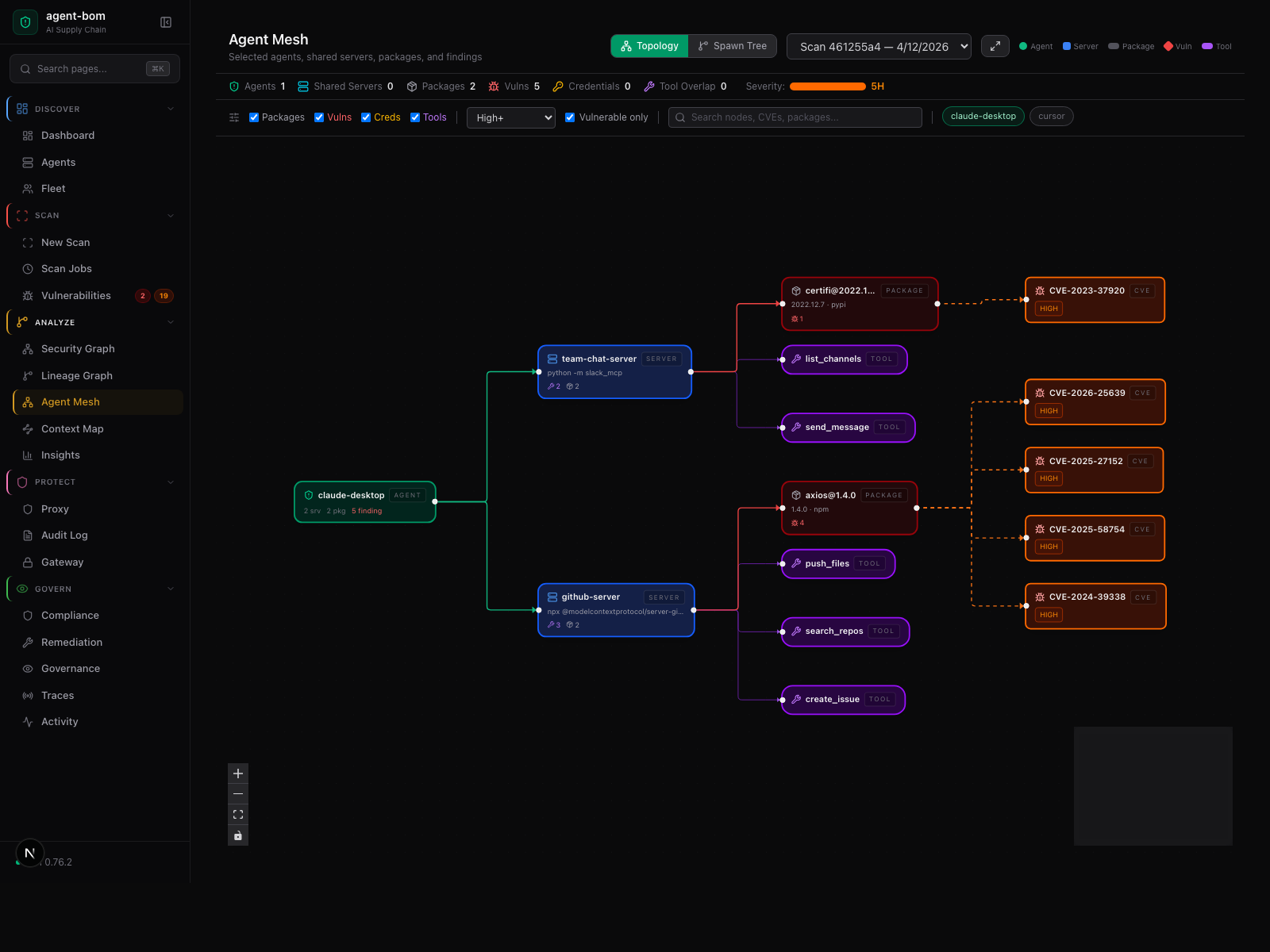
|── Cursor IDE (Agent · 4 servers · 12 tools)
|── ANTHROPIC_KEY, DB_URL, AWS_SECRET (Credentials exposed)
|── query_db, read_file, write_file, run_shell (Tools at risk)
Fix: upgrade better-sqlite3 → 11.7.0
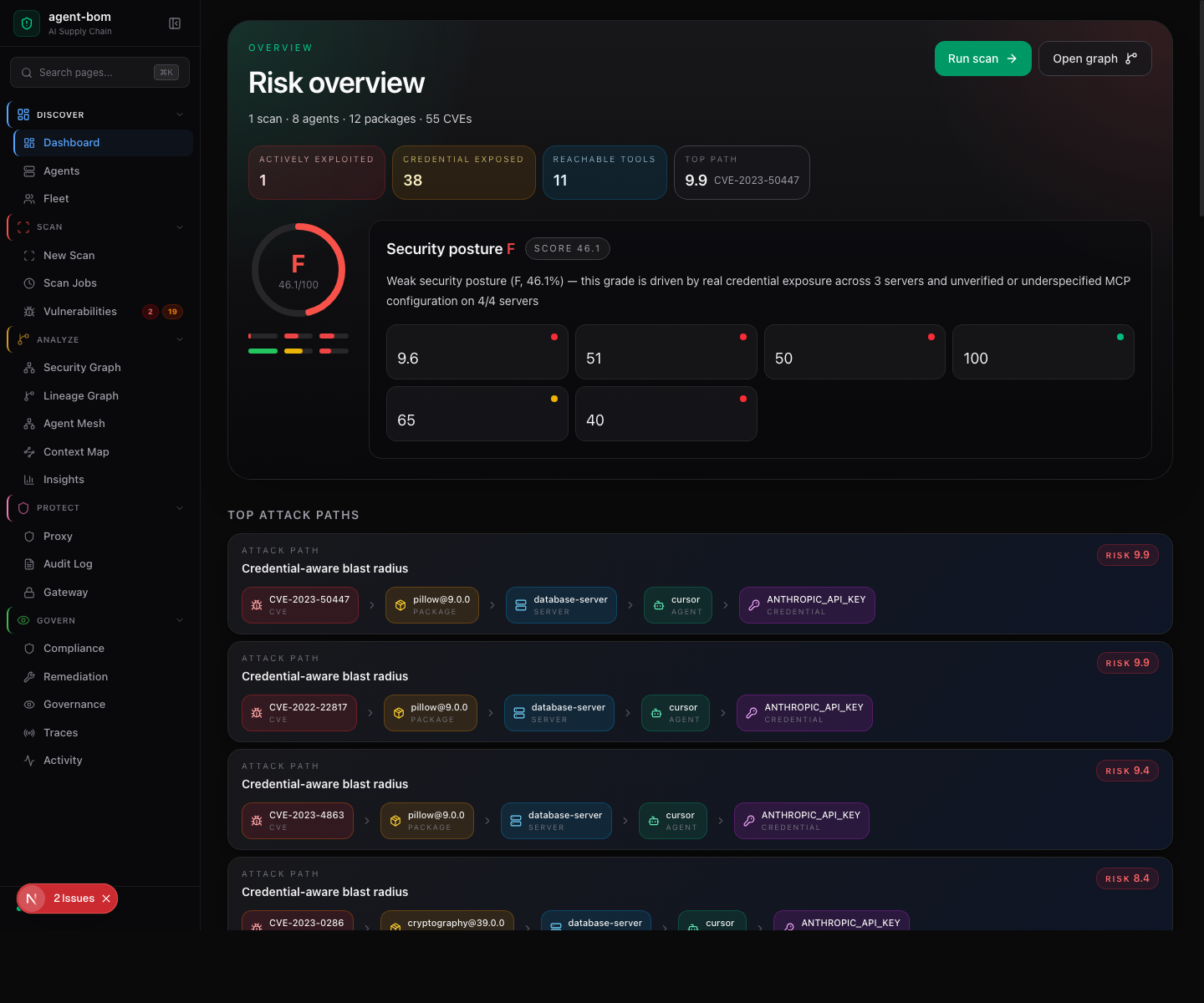
Blast radius is the core idea: CVE -> package -> MCP server -> agent -> credentials -> tools.
Scan local agent configs, MCP servers, instruction files, lockfiles, containers, cloud posture, GPU surfaces, and runtime evidence.
Try the built-in demo first:
agent-bom agents --demo --offlineThe demo uses a curated sample so the output stays reproducible across releases. For real scans, run agent-bom agents, or add -p . to fold project manifests and lockfiles into the same result.
pip install agent-bom
agent-bom agents -p . # Repo + MCP + package blast radius
agent-bom check [email protected] --ecosystem pypi # Pre-install package verdict
agent-bom image nginx:latest # Container image scan
agent-bom agents -p . --remediate remediation.md # Fix-first remediation plan
pip install 'agent-bom[ui]' # once, if you want the dashboard
agent-bom serve # API + dashboard + graph explorer- Agents + MCP — MCP clients, servers, tools, transports, trust posture
- Skills + instructions —
CLAUDE.md,AGENTS.md,.cursorrules,.windsurfrules,skills/* - Package risk — software supply chain scanning with enrichment and blast radius
- Container images + IaC — native OCI parsing plus Dockerfile, Terraform, CloudFormation, Helm, and Kubernetes coverage
- Cloud AI — cloud and AI infrastructure posture across major supported providers
- Secrets + runtime — MCP proxy, Shield SDK, secrets, and redaction surfaces
- Compliance + evidence — mapped governance plus ZIP evidence bundles for auditors
- Blast radius mapping — CVE → package → MCP server → agent → credentials → tools
- CWE-aware impact — RCE shows credential exposure, DoS does not
- Portable outputs — SARIF, CycloneDX, SPDX, HTML, graph, JSON, ZIP evidence bundles, and more
- MCP server mode — expose
agent-bomcapabilities directly to MCP clients like Claude, Cursor, Windsurf, and Cortex CoCo / Cortex Code - Skill bundle identity — stable bundle hashes for skill and instruction file review
- Dependency confusion detection — flags internal naming patterns
- VEX generation — auto-triage with CWE-aware reachability
Read-only. Agentless. No secrets leave your machine unless you explicitly enable an outbound integration.