Open security scanner for AI supply chain — agents, MCP servers, packages, containers, cloud, GPU, and runtime.
Start with the demo, then choose the entrypoint that matches your first job: repo scan, image scan, cloud posture, fix plan, dashboard, or runtime review.
CVE-2025-1234 (CRITICAL · CVSS 9.8 · CISA KEV)
|── [email protected] (npm)
|── sqlite-mcp (MCP Server · unverified · root)
|── Cursor IDE (Agent · 4 servers · 12 tools)
|── ANTHROPIC_KEY, DB_URL, AWS_SECRET (Credentials exposed)
|── query_db, read_file, write_file, run_shell (Tools at risk)
Fix: upgrade better-sqlite3 → 11.7.0
Blast radius is the core idea: CVE -> package -> MCP server -> agent -> credentials -> tools.
agent-bom scans local agent configs, MCP servers, instruction files, lockfiles, containers, cloud posture, GPU surfaces, and runtime evidence. CWE-aware impact keeps a DoS from being reported like credential compromise.
Try the built-in demo first:
agent-bom agents --demo --offlineThe demo uses a curated sample so the output stays reproducible across releases. For real scans, run agent-bom agents, or add -p . to fold project manifests and lockfiles into the same result.
Choose the view that matches what you need:
- CLI: fast local proof that blast radius and remediation are real
- Graph: one focused path first, then expand only when needed
- Dashboard: persistent state, diff, and review
Pick the entrypoint that matches your first job:
| Goal | Run | What you get |
|---|---|---|
| Find what is installed and reachable | agent-bom agents -p . |
Agent discovery, MCP mapping, project dependency findings, blast radius |
| Turn findings into a fix plan | agent-bom agents -p . --remediate remediation.md |
Prioritized remediation plan with fix versions and reachable impact |
| Check a package before install | agent-bom check [email protected] --ecosystem pypi |
Machine-readable pre-install verdict |
| Scan a container image | agent-bom image nginx:latest |
OS and package CVEs with fixability |
| Audit IaC or cloud posture | agent-bom iac Dockerfile k8s/ infra/main.tf |
Misconfigurations and posture findings |
| Review findings in a persistent graph | agent-bom serve |
API, dashboard, unified graph, current-state and diff views. Requires pip install 'agent-bom[ui]' once. |
| Inspect live MCP traffic | agent-bom proxy "<server command>" |
Inline runtime inspection, detector chaining, response/argument review |
pip install agent-bom # Standard CLI install
# pipx install agent-bom # Isolated global install
# uvx agent-bom --help # Ephemeral run without installing
agent-bom agents # Discover + scan local AI agents and MCP servers
agent-bom agents -p . # Scan project lockfiles/manifests plus agent/MCP context
agent-bom where # Show MCP discovery paths checked on this machine
agent-bom mesh --project . # Show the live agent / MCP topology
agent-bom skills scan . # Scan CLAUDE.md, AGENTS.md, .cursorrules, skills/*
agent-bom check [email protected] --ecosystem pypi # Pre-install CVE gate
agent-bom image nginx:latest # Container image scan
agent-bom iac Dockerfile k8s/ infra/main.tf # IaC scan across one or more pathsagent-bom agents -p . --remediate remediation.md # Fix-first plan with versions and reachable impact
agent-bom agents -p . --compliance-export fedramp -o evidence.zip # ZIP evidence bundle for auditors
pip install 'agent-bom[ui]' # once, for API + dashboard
agent-bom serve # Review the same findings in the dashboard and graphMore commands
agent-bom cloud aws # Cloud AI posture + CIS benchmarks
agent-bom agents -f cyclonedx -o bom.json # AI BOM / SBOM export
agent-bom check [email protected] -e pypi -f json # Machine-readable pre-install verdict
agent-bom report diff before.json after.json -f json # CI-friendly diff output
agent-bom agents -p . --compliance-export fedramp -o fedramp-evidence.zip # Auditor-ready evidence bundle
agent-bom graph report.json # Blast radius graph / graph HTML inputs
agent-bom proxy "npx @mcp/server-fs /ws" # MCP security proxy
agent-bom secrets src/ # Hardcoded secrets + PII
agent-bom verify agent-bom # Verify this installation
agent-bom verify [email protected] # Package integrity verification
agent-bom verify --model-dir ./models # Model weight hash verification
agent-bom serve # API + Next.js dashboard- Blast radius that maps
CVE -> package -> MCP server -> agent -> credentials -> tools - One operator path across CLI, CI, API, dashboard, remediation, and MCP tools
- AI-native coverage across agents, MCP, runtime, containers, cloud, IaC, and GPU surfaces
- Compliance evidence bundles for
cmmc,fedramp, andnist-ai-rmf
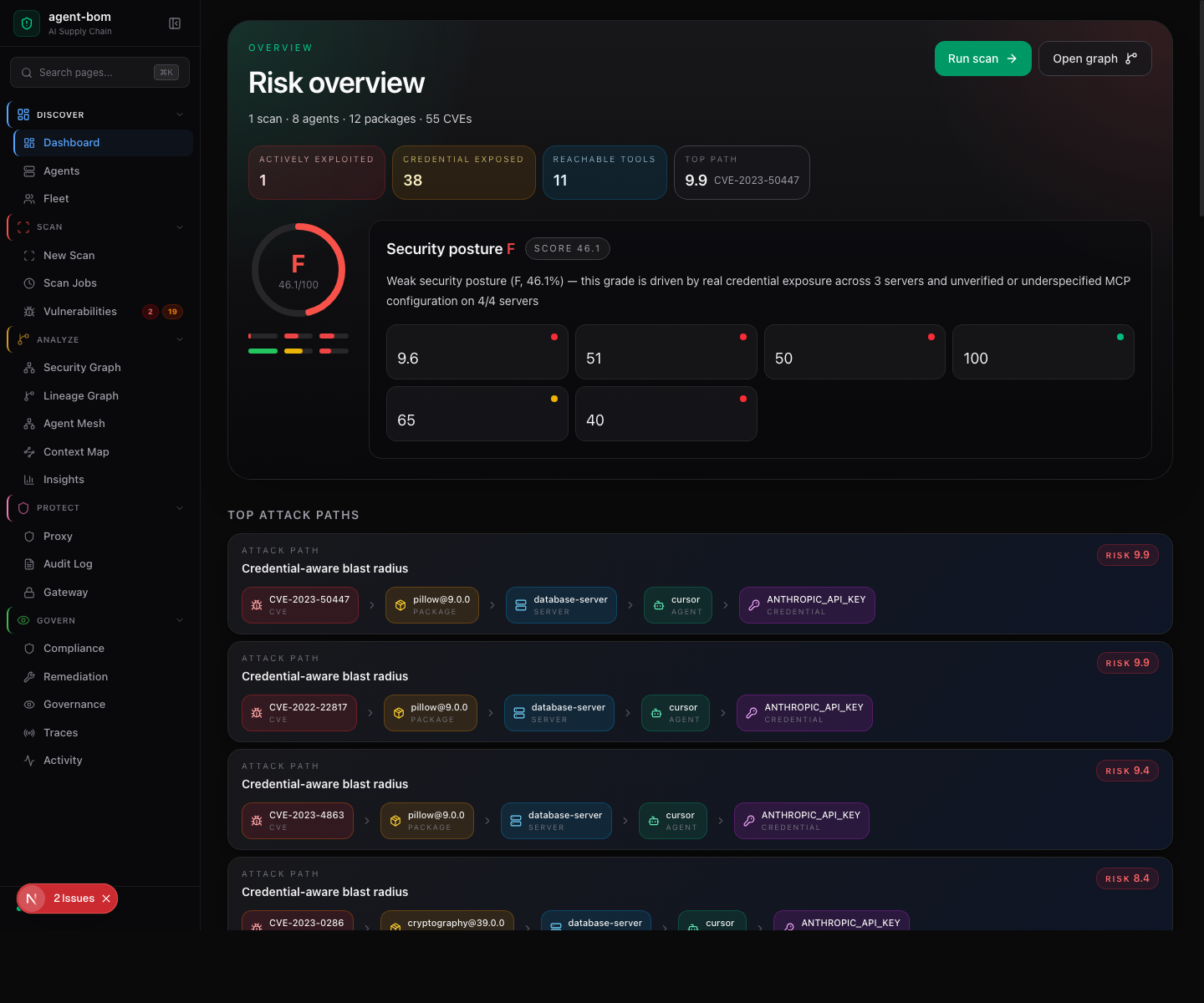
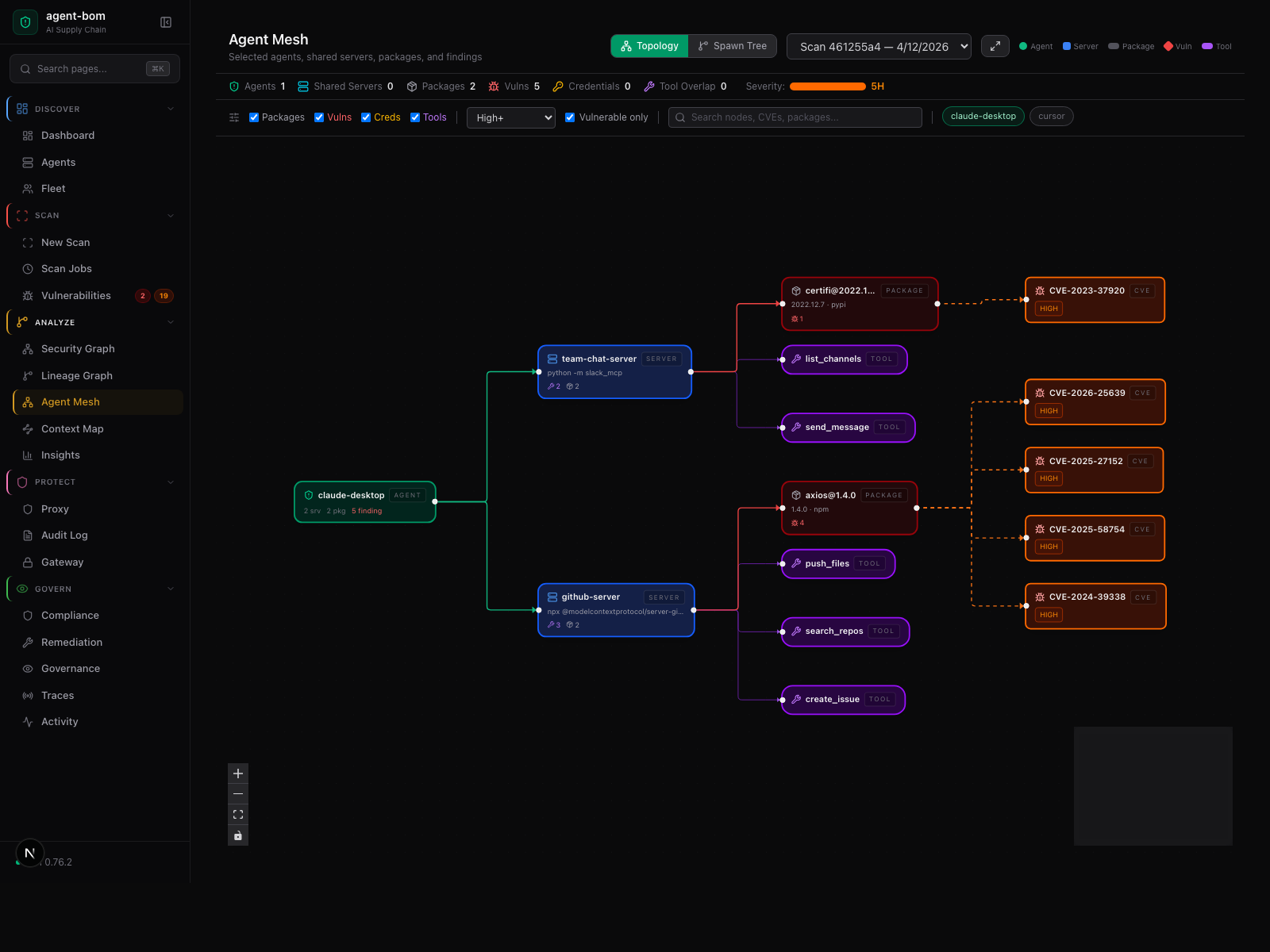
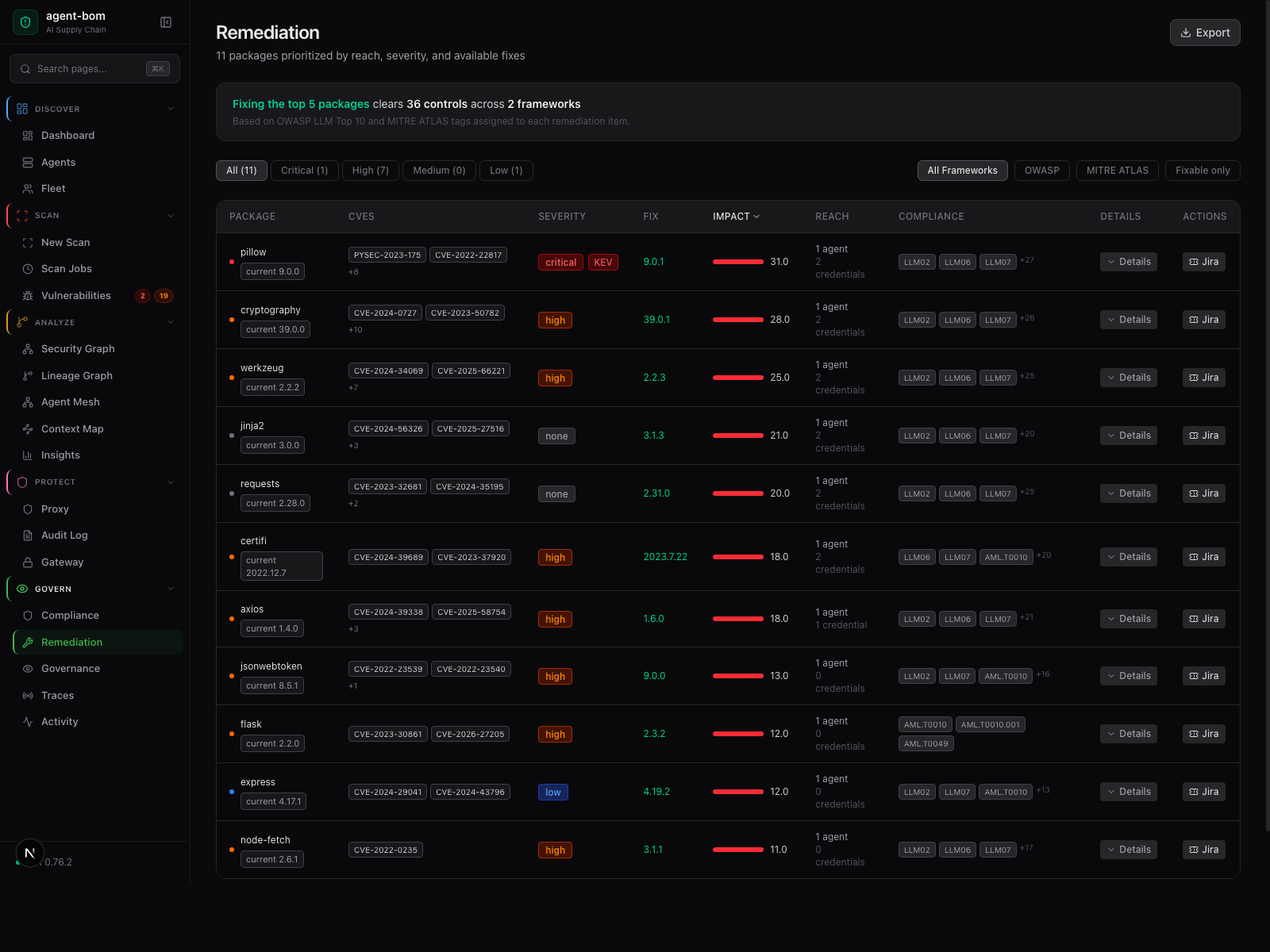
These screenshots come from the live product path, using the built-in demo data pushed into the API.
Risk summary, posture, and the highest-value attack paths without waiting on deep scan hydration.
The graph starts scoped to one agent and the vulnerable path in view, then expands only when the operator asks for more.
Reach, severity, fix version, and framework context stay in one review table so the operator can act without jumping between pages.
Default scans use the bundled MITRE ATT&CK + CAPEC catalog, so results stay deterministic and offline-friendly. Refresh to a newer upstream snapshot only when you want to:
agent-bom db update-frameworks
agent-bom db statusThe active catalog metadata is also surfaced in JSON output (framework_catalogs) and the API at /v1/frameworks/catalogs. Long-lived connected deployments can point at a synced catalog or opt into runtime refresh with AGENT_BOM_MITRE_CATALOG_MODE.
One path: discover, analyze, persist, then operate across CLI, CI, API, dashboard, and exports.

Blast radius stays explicit in the data model instead of being hand-waved as a generic finding list.

pip install agent-bom # CLI
docker run --rm agentbom/agent-bom agents # Docker| Mode | Command | Best for |
|---|---|---|
| CLI | agent-bom agents |
Local audit + project scan |
| GitHub Action | uses: msaad00/[email protected] |
CI/CD + SARIF |
| Docker | docker run agentbom/agent-bom |
Isolated scans |
| MCP Server | agent-bom mcp server |
Claude Desktop, Claude Code, Cursor, Codex, Windsurf, Cortex |
| Runtime proxy | agent-bom proxy |
MCP traffic enforcement |
| Shield SDK | from agent_bom.shield import Shield |
In-process protection |
| API + dashboard | agent-bom serve |
Fleet visibility, audit exports, and central review. Requires pip install 'agent-bom[ui]' once. |
Product references:
Use the GitHub Action when you want a fast CI gate: one step, one gate, SARIF in the Security tab, and a clean exit code for CI.
Repo + MCP + instruction files
- uses: msaad00/[email protected]
with:
scan-type: scan
severity-threshold: high
upload-sarif: true
enrich: true
fail-on-kev: trueContainer image gate
- uses: msaad00/[email protected]
with:
scan-type: image
scan-ref: ghcr.io/acme/agent-runtime:sha-abcdef
severity-threshold: criticalIaC gate
- uses: msaad00/[email protected]
with:
scan-type: iac
iac: Dockerfile,k8s/,infra/main.tf
severity-threshold: highAir-gapped / pre-synced CI
- uses: msaad00/[email protected]
with:
auto-update-db: false
enrich: falseDeveloper endpoints: runagent-bom agentslocally or via MDM for workstation inventory and posture.CI/CD: use the GitHub Action for PR gates, SARIF upload, image gates, and IaC checks.Central security team: deployagent-bom servefor fleet ingestion, posture, and audit exports.Air-gapped / isolated: run the Docker image with--offlineandauto-update-db: falseusing a pre-synced local DB.
See docs/ENTERPRISE_DEPLOYMENT.md for rollout patterns, auth models, and storage backends.
Install extras
| Extra | Command |
|---|---|
| Cloud providers | pip install 'agent-bom[cloud]' |
| MCP server | pip install 'agent-bom[mcp-server]' |
| REST API | pip install 'agent-bom[api]' |
| Dashboard | pip install 'agent-bom[ui]' |
Output formats
JSON, SARIF, CycloneDX 1.6 (with ML BOM), SPDX 3.0, HTML, Graph JSON, Graph HTML, GraphML, Neo4j Cypher, JUnit XML, CSV, Markdown, Mermaid, SVG, Prometheus, Badge, Attack Flow, plain text.
OCSF is currently used for runtime and SIEM event delivery, not as a general -f ocsf report format.
36 security tools available inside any MCP-compatible AI assistant:
{
"mcpServers": {
"agent-bom": {
"command": "uvx",
"args": ["agent-bom", "mcp", "server"]
}
}
}Also on Glama, Smithery, MCP Registry, and OpenClaw.
Trust & transparency
| When | What's sent | Where | Opt out |
|---|---|---|---|
Default CVE lookups (agents, scan, check, image) |
Package names + versions | OSV API | --offline |
| Floating version resolution | Package names, requested version/latest lookup | npm, PyPI, Go proxy | --offline |
--enrich |
CVE IDs | NVD, EPSS; KEV catalog download from CISA | Don't use --enrich |
--deps-dev |
Package names + versions | deps.dev | Don't use --deps-dev |
verify |
Package name + version | PyPI or npm integrity endpoints | Don't run verify |
| Optional push/integrations | Finding summaries or evidence bundles | Slack, Jira, Vanta, Drata | Don't pass those flags |
No source code, config contents, or credential values are sent. No telemetry or analytics. Sigstore-signed releases. See SECURITY_ARCHITECTURE.md and PERMISSIONS.md for the full trust model.
git clone https://github.com/msaad00/agent-bom.git && cd agent-bom
pip install -e ".[dev-all]"
pytest && ruff check src/See CONTRIBUTING.md | docs/CLI_DEBUG_GUIDE.md | SECURITY.md | CODE_OF_CONDUCT.md
Apache 2.0 — LICENSE
Resources
agent-bom Scan is not certified by GitHub. It is provided by a third-party and is governed by separate terms of service, privacy policy, and support documentation.